Skip to content
Watch, Read, Listen
- 20 Easy Methods for Reducing Stress: A Roadmap to Inner Peace
by Nikhil Satish Pawar
- Understanding the Movie “Waves”
by Nikhil Satish Pawar
- Love What You Have, Before Life Teaches You to Love — Tymoff
by Nikhil Satish Pawar
- 100 quotes that change your life with Photos
by Nikhil Satish Pawar
- The 10 Best ‘Oppenheimer’ Movie Quotes
by Nikhil Satish Pawar
- 10 phrases to use when your toddler doesn ‘t listen
by Nikhil Satish Pawar
- If you use these 10 phrases regularly, you have very high level of emotional intelligence
by Nikhil Satish Pawar
- 10 Signs Your Partner Loves You Unconditionally: A Psychologist’s Guide
by Nikhil Satish Pawar
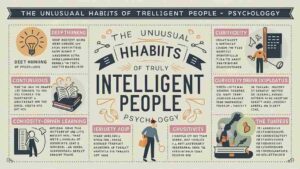
- 10 Unusual habits of truly intelligent people, according to psychology
by Nikhil Satish Pawar
- How to Be a Good Friend
by Nikhil Satish Pawar
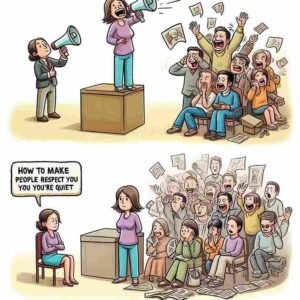
- How To Make People Respect You If You’re Quiet
by Nikhil Satish Pawar
- Can a long distance relationship work?
by Nikhil Satish Pawar